Cybersecurity Fundamentals: Why Tools Aren’t Enough Without Human Understanding
The fundamentals of cybersecurity are about protecting an organization’s assets from threat actors who use tools and exploits to execute tactics, techniques, and procedures (TTPs) that produce malicious outcomes, such as unauthorized access, disruption, fraud, or data theft.

The fundamentals of cybersecurity are simple to say, but hard to do well: protect an organization’s assets from threat actors.
Those threat actors don’t “hack” in a single move. They use tools and exploits to execute tactics, techniques, and procedures (TTPs) that lead to real outcomes, unauthorized access, disruption, fraud, and data theft.
And the hard truth is this: there are thousands of active threat actors globally, and they constantly evolve. They adapt faster than static controls. They borrow playbooks, improve them, and test them against real environments every day.
That’s why security can’t be built on the fantasy of defending against everything at once.
Security Isn’t About Defending Against Everything
No organization can realistically anticipate and stop every technique in real time.
Effective security is about:
- understanding which threats are most likely for your sector
- knowing what your technology stack exposes
- focusing on attack paths that are realistic for your environment
- maintaining strong baseline controls that reduce risk across many paths
This is not “lowering standards.” It’s how mature security programs survive reality.
Why Threat Landscape Awareness Is Non-Negotiable
To prioritize correctly, an organization needs continuous awareness of the threat landscape, including:
- which actors are active
- what TTPs they are using right now
- which vulnerabilities (CVEs) they exploit
- what tooling and infrastructure supports their campaigns
When teams learn from real-world activity and trends, they can:
- prioritize controls that matter
- strengthen detection and response
- spend resources where impact is highest
Without this awareness, security becomes guesswork.
Automation Helps But Humans Still Decide
Automation is powerful. Security tools can:
- collect signals
- enrich context
- score risk
- correlate events
- trigger workflows
But automation is not the final authority, humans are.
A human remains the final judge because they must:
- validate intent
- separate false positives from real incidents
- decide business impact
- choose the right response under uncertainty
This “human-in-the-loop” role matters because attackers deliberately exploit what automated systems struggle with most:
- context
- logic gaps
- assumptions
- edge cases
- ambiguity
In other words: attackers don’t just fight your tools. They fight your understanding.
The CTI Gap: Strong Platforms, Weak Learning
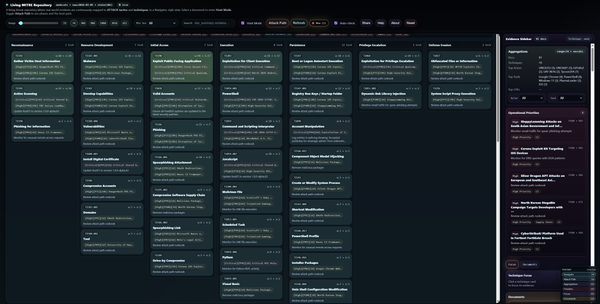
Many CTI platforms are designed primarily around:
- feeds
- correlation
- alerting
- ticketing
- dashboards
All useful, but often not enough.
The missing piece is education.
Education in CTI does not mean longer reports. It means helping analysts and decision-makers understand real attacks through structured breakdowns, such as:
- mapping adversary behavior to ATT&CK-style techniques
- linking exploited CVEs to real exposure
- tying observed activity directly to defensive controls
And it means delivering that understanding through experience, not just text:
- interactive visualizations (attack timelines, technique graphs, relationship maps)
- guided workflows that lead analysts through the “why” and “how”
- chat-based assistants that can explain:
- why this matters
- how it happened
- what to do next
When CTI becomes understandable, it becomes usable.
What Happens When Education Is Missing
When education is missing, organizations fall into a dangerous imbalance:
- strong tooling
- weak human understanding
The result is predictable:
- teams react faster, but don’t improve
- alerts get handled, but root causes repeat
- lessons learned don’t turn into strategy
- intelligence exists, but doesn’t change decisions
Tools can accelerate work.
Only educated humans can adapt strategy as the threat landscape changes.
The Problem Lidar Kinesis Is Built to Solve
This is the problem Lidar Kinesis is built to solve.
Not just collecting and correlating threat data, but translating it into understanding:
- mapping attacks to standardized frameworks
- enriching context around actors, TTPs, and CVEs
- presenting intelligence through interactive views
- providing conversational guidance so teams learn faster
The goal is simple:
help teams learn faster, respond smarter, and adapt continuously, because the threat landscape never stands still.