From Assets to Action: How a Modern Cybersecurity Program Actually Works
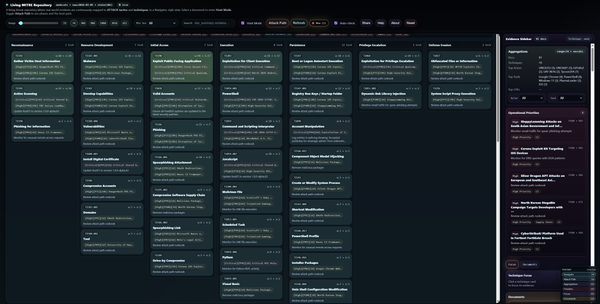
The diagram below explains a mature, real-world cybersecurity program where decisions are driven by business goals, risk, and intelligence, not by technology alone


Most cybersecurity diagrams fail because they present security as a collection of tools rather than a connected system. The diagram explained in this article represents a mature, real-world cybersecurity program where decisions are driven by business goals, risk, and intelligence, not by technology alone. It shows how governance, threat modeling, cyber threat intelligence, and security operations are tightly integrated into a continuous cycle of learning and improvement.
Business Goals and Governance as the Starting Point
Every effective cybersecurity program begins with business goals. Security exists to protect what enables the organization to function, generate revenue, and maintain trust. Availability, integrity, confidentiality, and compliance are business outcomes, not technical features.
Governance, Risk, and Compliance provides the structure that allows security to operate. Governance defines ownership, classification, risk appetite, escalation paths, and legal authority. Without this layer, security teams either overreact or hesitate, both of which increase risk. Governance ensures that every security decision is aligned with what the business can tolerate and what it must protect at all costs.
Asset Management as the Foundation of Defense
Asset management is the first operational step in the program. Assets are clearly categorized into people, hardware, software, networks, and data. Each category introduces different risks and requires different controls.
From these asset categories, specific security domains emerge, such as endpoint security, network security, application security, data security, physical security, and security awareness. This structure ensures that protection is systematic rather than ad hoc. If assets are incomplete, outdated, or poorly classified, every downstream security activity becomes unreliable.
Threat Modeling as the Intelligence Pivot
Threat modeling sits immediately after asset management because it transforms inventory into understanding. It answers fundamental questions about how real attackers could compromise specific assets in the given environment.
This stage identifies realistic threats, relevant vulnerabilities, and plausible attack paths. Instead of attempting to defend against everything, the organization focuses on what is most likely and most damaging. Threat modeling prevents tool-driven security and replaces it with attacker-centric thinking.
Red Teaming and Vulnerability Assessment as Reality Checks
Red team activities and vulnerability assessments test the assumptions made during threat modeling. Red teams simulate adversaries and evaluate not only technical controls but also detection, response, and human decision-making. Vulnerability assessments and penetration testing identify weaknesses that are actually exploitable, not just theoretically present.
The key outcome of this stage is validated vulnerabilities. These findings are not treated as isolated reports but are fed directly into risk assessment and intelligence processes.
Risk Assessment as the Decision Engine
Risk assessment is where technical findings are translated into business decisions. It combines validated vulnerabilities, threat intelligence, asset criticality, and business impact to determine what truly matters.
This stage prioritizes remediation, identifies acceptable risks, and highlights areas that require monitoring rather than immediate action. Risk assessment ensures that security resources are applied where they reduce risk most effectively, rather than being driven by volume or severity scores alone.
Controls as Risk-Driven Outcomes
Controls are implemented because risk demands them, not because a product exists. Preventive controls reduce the likelihood of compromise. Detective controls generate visibility through logs and detections. Responsive controls enable containment, investigation, and recovery.
Controls are continuously refined based on intelligence, incidents, and changing business priorities. They are not static and should never be deployed without a clear risk justification.
Blue Team and Security Operations as Execution
The Security Operations Center represents the execution layer of the program. Telemetry flows from assets into logs, from logs into the SIEM, from alerts into incidents, and from incidents into investigations and digital forensics.
Playbooks guide response actions, while incident response and forensic activities generate lessons learned. The SOC does not decide what matters most; it operationalizes decisions that have already been shaped by risk, governance, and intelligence.
Cyber Threat Intelligence as the Force Multiplier
Cyber Threat Intelligence acts as the shared memory and analytical backbone of the entire program. The internal CTI repository aggregates threat actors, attack techniques, exploited vulnerabilities, indicators, and contextual intelligence.
CTI enriches alerts, supports investigations, improves detections, informs threat modeling, and strengthens risk assessment. It connects external threat activity with internal exposure, allowing the organization to anticipate attacks rather than simply react to them.
Continuous Learning and Program Evolution
The cybersecurity program shown in this diagram is not linear. Incidents feed back into threat modeling. Threat intelligence updates risk assessments. Risk reshapes controls. Controls generate new telemetry. Telemetry improves detection and response.
Over time, the organization becomes more resilient because it learns from both attacks and near-misses. This continuous feedback loop is what separates a mature cybersecurity program from one that only reacts after damage occurs.
Conclusion
This diagram illustrates that effective cybersecurity is a system, not a stack of tools. Assets define what must be protected. Threat modeling explains how it can be attacked. Risk determines what matters most. Governance enables action. Intelligence provides context. Operations execute decisions.
When these elements work together, security becomes intentional, measurable, and aligned with business reality rather than reactive and fragmented.