From Static Threat Reports to a Living Threat Map
Cybersecurity has produced an enormous amount of intelligence over the years: reports, CVE advisories, blog posts, breach disclosures, incidents, and vendor threat research. Every week, hundreds of new documents appear describing attacks, malware campaigns, vulnerabilities, and threat actors.

But there is a fundamental problem. Most of this intelligence is static.
A PDF report is published.
A blog post is released.
An advisory is shared.
And then the information disappears into archives, bookmarks, and threat feeds. Security teams read it once, maybe extract a few indicators, and move on. From a first-principles perspective, this is inefficient.
Threat intelligence is not valuable because it exists.
Threat intelligence is valuable only when it improves defensive decisions.
If intelligence cannot translate into real work such as:
- detection engineering
- threat hunting
- security architecture decisions
- defensive prioritization
then the intelligence loses most of its value.
The problem is not the intelligence itself.
The problem is how it is structured, accessed, and used.
Security Defends Against Behavior (Not Headlines)
At its core, cybersecurity defense exists to stop attacker behavior.
Not headlines.
Not articles.
Not vendor reports.
Attackers perform actions such as:
- scanning infrastructure
- exploiting vulnerabilities
- establishing persistence
- communicating with command-and-control servers
- exfiltrating data
The MITRE ATT&CK framework exists because it models these behaviors. Instead of describing attacks as stories, it describes them as techniques. For example:
- T1190 – Exploit Public-Facing Application
- T1071 – Application Layer Protocol
- T1547 – Boot or Logon AutoStart Execution
These techniques represent what attackers actually do.
So if we want to learn from incidents efficiently, the natural approach is to map real-world attacks to these behaviors.
The Problem With Traditional Intelligence Consumption
Most teams consume intelligence in formats like:
- news articles
- threat reports
- vulnerability bulletins
- security advisories
- vendor research papers
These formats are valuable, but they create three predictable operational problems.
1) Intelligence Is Narrative, Not Structured
A report might say:
“The attacker exploited a public-facing application and established persistence.”
But the report rarely translates that into direct, consistent technique IDs like:
- T1190 (Initial Access)
- T1547 (Persistence)
So analysts must manually convert narratives into actionable technical steps.
That conversion is expensive.
It requires experience.
It causes inconsistency.
And it’s slow.
2) Knowledge Becomes Fragmented
Teams often store intelligence in:
- spreadsheets
- bookmarks
- Slack threads
- ticket systems
- SIEM notes
Over time, the knowledge becomes scattered.
Two analysts may read the same report and remember different details.
A third analyst joins later and can’t reconstruct what mattered.
A detection engineer wants “the technique list” and can’t easily extract it.
The organization ends up with intelligence that is present but not usable.
3) Intelligence Is Not Connected to Defensive Workflows
When detection engineers or threat hunters do real work, they usually start from:
- ATT&CK Navigator
- SIEM logs
- endpoint telemetry
- network telemetry
But the connection between real incidents and these workflows is weak.
This creates the most damaging gap of all:
Threat intelligence stays in “reading space”
while security operations live in “doing space”.
A Living Threat Map (What Changes If We Fix the Structure)
Instead of treating intelligence as documents, we can treat it as structured knowledge linked to attacker behavior.
That is the idea behind a Living MITRE Repository.
A living repository continuously ingests threat reports and converts them into structured intelligence mapped directly to ATT&CK techniques.
The result is a system where:
- incidents are connected to techniques
- techniques accumulate real-world evidence
- analysts can pivot quickly between intelligence and behavior
- patterns emerge across incidents (instead of isolated reading)
Instead of reading one report at a time, defenders gain a continuously evolving view of how attackers actually operate.
How the Living MITRE Repository Works (In Practical Terms)
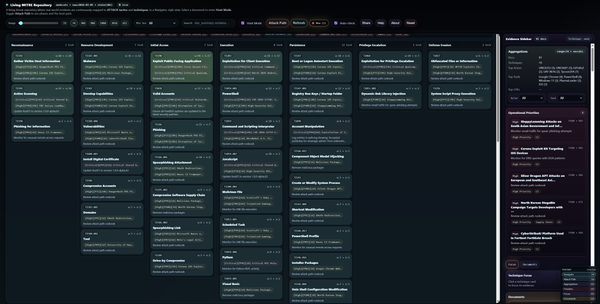
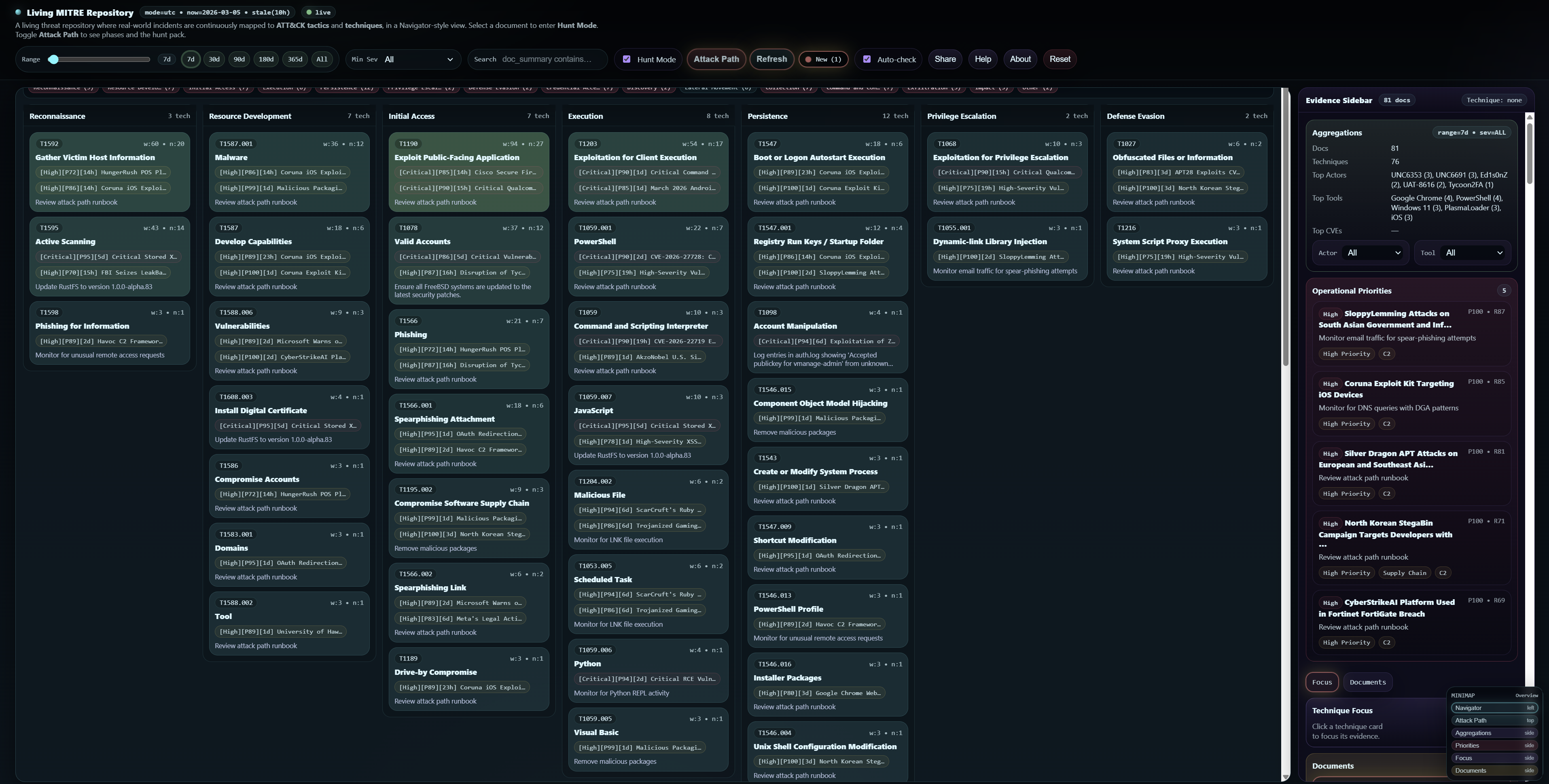
The platform transforms traditional threat intelligence into a Navigator-style investigation interface.
It is built around how analysts actually work: filter → pick evidence → understand behavior → act.
The interface is organized into four main areas
Documents (your starting point)
This is the report library. It shows all reports that match your current filters (time range, severity, keyword search, actor/tool pivots, etc.).
If you’re new, start here.
Navigator (left panel)
This is the ATT&CK map. Techniques are grouped by tactics (Initial Access, Execution, Persistence, Command and Control, Exfiltration, etc.).
This is where you see “behavior at scale”.
Evidence Sidebar (right panel)
This is the “why and proof” area. It shows what the selected evidence contains: summary, actors, tools, CVEs, extracted entities, and details that support the mapping.
Attack Path + Hunt Pack (action workflow)
This is where intelligence becomes operations. It turns an incident into stages, checks, detection hints, remediation steps, and pivots.
What You See in the Navigator (And Why It Matters)
At the center of the platform is the Navigator view. Each column represents an ATT&CK tactic, such as:
- Reconnaissance
- Initial Access
- Execution
- Persistence
- Command and Control
- Exfiltration
Inside each tactic column are technique cards. Each technique card shows:
- the technique ID
- the technique name
- how often it appears (evidence frequency across incidents)
- supporting evidence from real-world incidents
This is important because it changes how you “read intelligence”.
Instead of reading a story, you see a behavior map. Instead of remembering one report, you see repeated technique patterns across many incidents.
From Intelligence to Action (Hunt Pack)
The platform does more than display mappings.
Each incident generates an analyst-focused Hunt Pack designed to answer:
“What do I do next?”
The Hunt Pack includes:
Threat Brief
A concise summary of the incident in plain language.
Checks Now
Immediate detection opportunities defenders should verify today.
Phase Runbook
A structured breakdown of each attack stage, including:
- what the attacker did
- what defenders should monitor
- remediation steps
Intelligence Pivots
Quick filters that allow analysts to explore related incidents by:
- threat actor
- tool / malware
- CVE
- infrastructure indicators
- sector / geography / software
Coverage & Gaps
A simple assessment of whether key indicators are missing from the intelligence.
Exfiltration & Impact Watch
Signals that may indicate data theft or operational damage.
This is the key idea:
You don’t just “learn” from the incident.
You can immediately convert it into a workflow.
A Beginner Workflow (How to Use the Platform Without Getting Lost)
If you’re a student or a first-time user, follow this simple flow:
Start at the top bar and set your scope:
- choose a time range (7d / 30d)
- set minimum severity (Moderate+ / High+)
- optionally type a keyword in search
Then go to the Documents panel and pick one report.
That report becomes your starting evidence.
Enable Hunt Mode.
Now the Navigator highlights the techniques used in that selected report.
Click Attack Path.
Now you see the incident as a staged progression (not just scattered techniques).
Open the Hunt Pack.
Pick two “Checks Now” items and translate them into “what logs do I check?”
- SIEM queries
- EDR telemetry
- firewall/proxy logs
- cloud audit logs
That is the operational bridge most intelligence fails to provide.
Why This Matters for Security Teams (The Compounding Effect)
The value of a Living MITRE Repository shows up in three benefits.
Intelligence Becomes Operational
Instead of reading passively, analysts can immediately see:
- what techniques were used
- where detection opportunities exist
- how the attack progressed
This closes the gap between threat intelligence and SOC operations.
Knowledge Compounds Over Time
Each new incident adds evidence to techniques. Over time, the repository becomes a behavioral knowledge base, where defenders can see:
- recurring techniques
- tool reuse
- actor behavior trends
- emerging patterns across time windows
Static intelligence disappears.
Living intelligence accumulates.
Threat Hunting Becomes Faster
Traditional threat hunting often requires analysts to manually connect intel to behavior.
With a living repository, the mapping already exists. Analysts can pivot quickly from:
an incident → techniques
a technique → related incidents
an actor → behavior patterns
This reduces investigation time and increases consistency.
Why the Repository Is “Living”
The key difference between this platform and static reports is that it continuously evolves.
As new incidents are added:
- technique statistics update
- pivots expand
- patterns become visible
- “what’s trending” becomes measurable
The repository becomes a living record of attacker behavior, not a library of disconnected documents.
Designed for Analysts (Not Just for Viewing)
The platform is intentionally designed around the way analysts work:
- ATT&CK Navigator-style visualization
- fast document switching (keyboard + quick search)
- document-centric hunting workflows
- phase-based attack path analysis
- pivot-driven investigation
- shareable view for team coordination
The goal is simple:
Reduce friction between reading intelligence and doing security work.
Open Intelligence Infrastructure (Why This Can Grow With You)
Another principle behind the project is transparency and extensibility.
Organizations should be able to integrate:
- their own threat feeds
- internal incident reports
- vulnerability intelligence
- external research
This transforms intelligence from “static content” into operational knowledge infrastructure.
A Shift in How We Use Intelligence
For decades, cybersecurity has treated threat intelligence as something we read. But intelligence should not simply be read.
It should be interacted with.
Explored.
Filtered.
Mapped.
Operationalized.
By mapping real incidents directly to attacker behaviors, a Living MITRE Repository turns threat intelligence into something far more powerful:
A continuously evolving map of how attackers actually operate. And in cybersecurity, understanding behavior is the foundation of defense.
Visit the platform