Threat Library: Asset-Relevant Threat Intelligence, Supercharged by AI
Most threat intel platforms tell you what’s happening in the world. Threat Library tells you what’s happening to your products and then uses AI to convert that intelligence into actionable decisions for Blue Teams, Red Teams, and leadership.

Most threat intelligence platforms tell you what’s happening in the world.
Threat Library tells you what’s happening to your products, and then uses AI to convert that intelligence into decisions and actions for your SOC.
In other words: it’s not “interesting news.” It’s operational intelligence, mapped to your organization’s stack.
The Problem: Global Intel Isn’t Automatically Relevant
Security teams are flooded with reports:
- A new APT campaign here
- A new critical CVE there
- A new malware family trending somewhere else
But the hard question remains:
Does this impact the vendors and products we actually run?
If your intel isn’t aligned to your assets, it becomes noise.
The Approach: Start With What You Own
Threat Library begins with a simple but powerful step:
Asset onboarding defines relevance
An organization onboards:
- Vendors
- Products / assets
- (optionally) criticality, exposure, ownership, environment tags
This creates an Asset Relevance Baseline:
“This is what we care about. Prioritize anything that touches it.”
Continuous Threat Streams + Rich Enrichment
Once onboarding is done, the platform continuously ingests threat streams and incident intelligence.
But it doesn’t store them as raw text.
It enriches and structures them into usable context, including:
- Threat actors / clusters
- CVEs and exploit mentions
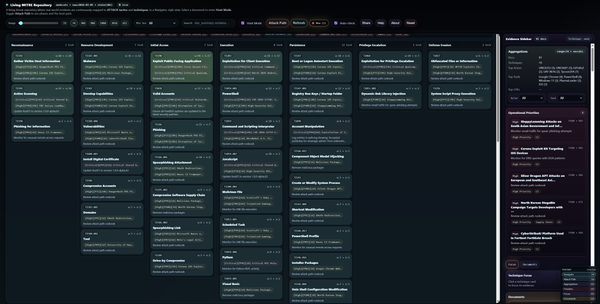
- Tools, malware families, infrastructure
- TTPs and MITRE techniques
- Access vectors, targeted assets, data types at risk
- Representative evidence samples with drill-down navigation
The Result: A Living Threat Library Per Product
Every time intelligence mentions an onboarded product, it becomes attached to that asset.
Over time, this compiles into a living threat library for each product:
- what’s trending now
- what’s repeatedly exploited
- which actors target it
- which tools and TTPs show up most often
- which vulnerabilities appear frequently
- what access vectors are being used
- how risk evolves over time
This creates a simple outcome:
Threat intelligence becomes relevant automatically.
Where AI Adds Real Value
Threat Library doesn’t use AI to “chat.”
It uses AI to convert structured intelligence into decisions.
1) AI Threat Model Per Product (SOC-ready)
For any product row, AI generates a readable report:
- Executive summary
- Risk level + score + confidence
- Why this matters
- Likely adversaries
- Attack surface
- Key threats
- MITRE techniques mapping
- Control gaps and recommended controls
- Analyst next steps
- Detection ideas (SOC-friendly)
This is designed for operations, not marketing summaries.
2) AI Risk Assessment (for prioritization)
AI adds a risk lens leadership can act on:
- likelihood / impact
- why the product is under pressure (drivers)
- what to do now vs later
- where controls are weak
- where mitigation gives the fastest reduction in risk
So you can answer:
“Which products are under the most pressure this quarter, and what do we do first?”
3) AI with Cost Control (Cache-first)
Real SOC environments need predictable spend.
So AI output is cached per entity and reused:
- instant access for analysts
- reduced OpenAI cost
- consistent outputs over time
4) AI Freshness Awareness (Staleness Detection)
Threat streams never stop, and AI must never pretend it’s current.
Threat Library stores a snapshot at generation time:
- last activity timestamp
- incident counts
When new evidence arrives, the UI marks the report:
- AI Cached (stale) and offers one click:
- Regenerate (only when needed)
So you get:
- speed of caching
- honesty about freshness
- control over cost
5) AI-Assisted Investigation (Dive Search + Conversate)
Analysts can highlight any text on the page (actors, CVEs, tools, techniques) and instantly:
- collect terms into a tray
- run Dive to retrieve contextual results
- run Conversate to ask targeted questions using selected terms
This creates a workflow SOC analysts love:
Select → Investigate → Understand → Act
Who This Helps (and Why)
Blue Teams (SOC / Detection / IR)
- prioritize hunting and detections by relevance to your stack
- reduce noise and focus on products you actually operate
- use actors/CVEs/tools/TTPs for faster triage and better playbooks
Red Teams / Purple Teams
- use the threat library as a realistic “attack playbook”
- simulate what’s trending against your real technology
- align red and blue priorities using the same intelligence base
Leadership (CISO / Risk / Governance)
- see risk pressure by product and vendor
- drive patch acceleration and compensating controls
- make investment decisions grounded in real external activity
The Differentiator
Most platforms are “intel feeds.”
Threat Library is:
An AI-powered asset-relevant threat intelligence engine.
It continuously maps global incidents to your onboarded products, enriches them with actors/CVEs/tools/TTPs, and generates cached, freshness-aware threat models and risk assessments, enabling proactive defense and faster SOC decision-making.